The End of the Privacy Paradox: Mastering Data with Privacy-Enhancing Technologies (PETs)
For the last decade, organizations have faced a grueling “Privacy Paradox.” On one hand, data is the lifeblood of innovation—vital for medical research, fraud detection, and personalized services. On the other hand, the risk of data breaches and the tightening grip of global regulations like GDPR and CCPA have made holding sensitive data a massive liability.
In 2026, we are finally solving this paradox. The emergence of Privacy-Enhancing Technologies (PETs) is fundamentally changing the rulebook: Organizations can now extract the full value of data without ever actually seeing, touching, or decrypting the sensitive information itself.
1. What are PETs? The “Invisible” Data Revolution
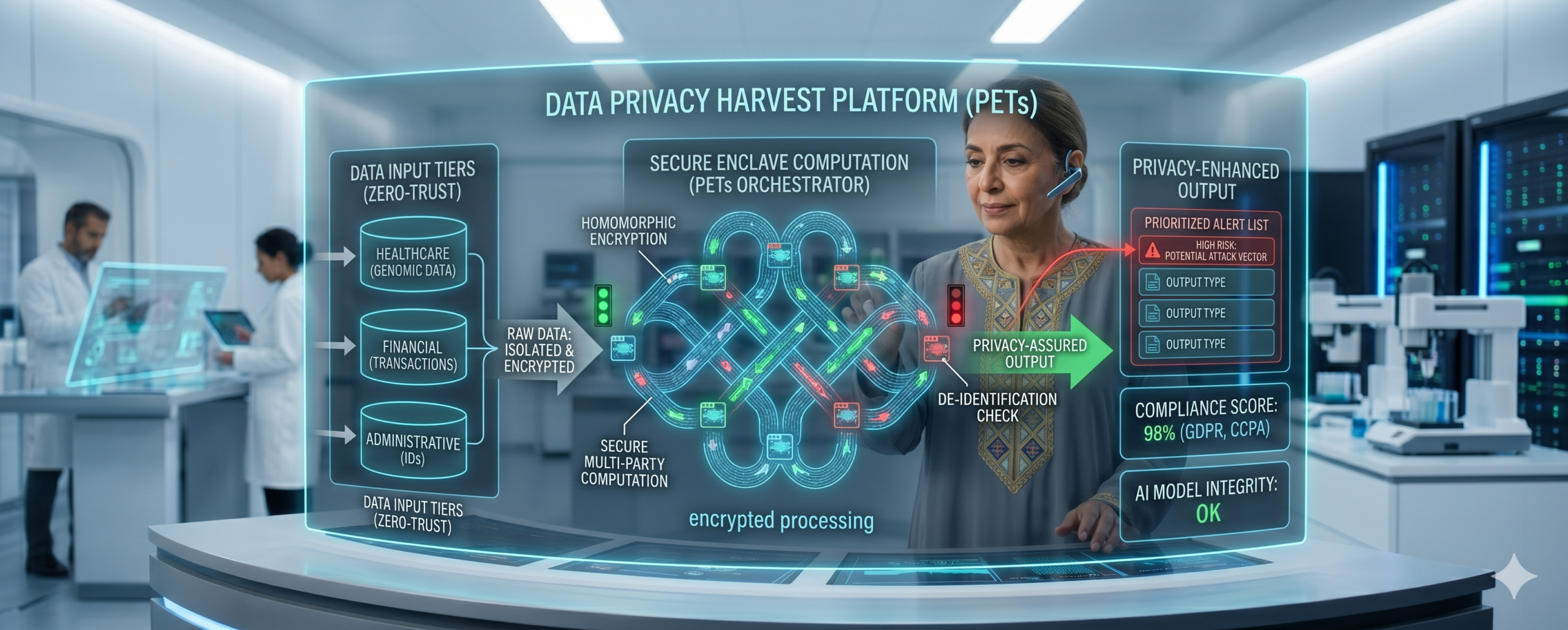
PETs are a suite of mathematical and technical tools designed to protect data privacy throughout its entire lifecycle—not just while it sits in a database, but while it is actively being used.
Traditionally, to analyze data, you had to decrypt it, creating a “window of vulnerability.” PETs close that window permanently.
The Holy Grail: Homomorphic Encryption (HE)
The most transformative of these technologies is Fully Homomorphic Encryption. In standard encryption, if you want to add two numbers ($x + y$), you must decrypt them first. With HE, you can perform mathematical operations on the encrypted data itself.
The result is an encrypted output that, when decrypted by the owner, provides the correct answer. The server performing the work never knows what the numbers were, or even what the final answer is.
2. Secure Multi-Party Computation (SMPC)
While HE is about computing on one dataset, SMPC is about collaboration without trust. SMPC allows multiple parties to jointly compute a function over their inputs while keeping those inputs private from each other.
Case Study: Financial Fraud Detection
Imagine three rival banks. They all want to catch a sophisticated money launderer moving funds between them, but they cannot legally share their customer data with one another. Using SMPC, the banks can run a collective “fraud check” algorithm. The system flags the suspicious pattern across all three banks, but none of the banks ever see each other’s private customer lists.
3. Synthetic Data: The Secure Sandbox
Not all privacy solutions require complex math on live data. Synthetic Data uses AI (Generative Adversarial Networks) to create an entirely fake dataset that maintains the exact statistical properties of the original.
For a data scientist, synthetic data looks and acts exactly like real patient records or credit card transactions. However, because the individuals in the dataset do not actually exist, there is zero risk of a privacy leak. This allows healthcare research teams to share “data” globally without violating a single privacy law.
4. Differential Privacy: Noise as a Shield
Differential Privacy is a technique used by companies like Apple and Google to collect “crowdsourced” data without identifying individuals. It works by adding a mathematically calculated amount of “noise” to the data.
If a researcher looks at the group as a whole, the trends are 100% accurate. But if they try to zoom in on a single person, the “noise” makes it impossible to tell who that person is. It provides a mathematical guarantee that an individual’s presence in a dataset cannot be determined.
5. The Business Case for PETs
Adopting PETs is no longer just a compliance checkbox; it is a competitive advantage.
- Zero-Trust Data Sharing: Collaborate with competitors or third parties without revealing trade secrets.
- Global Compliance: Move data across borders (sovereignty) by ensuring the data is mathematically “not personal” during transit.
- Brand Trust: Tell your customers: “We don’t just protect your data; we physically cannot see it.”
Conclusion: Privacy by Mathematics
In 2026, the hallmark of a professional, forward-thinking organization is the transition from “Privacy by Policy” (hoping people follow rules) to “Privacy by Design” (using math to make a breach impossible).
As PETs become more computationally efficient, they will become the standard for every data interaction. At RTC, we help you navigate this complex mathematical landscape, turning your data from a liability into a secure, private engine for growth.
Is Your Team PET-Ready?
- Audit: Identify which datasets are too sensitive to share but too valuable to ignore.
- Experiment: Start with Synthetic Data for your testing and development environments.
- Scale: Implement Homomorphic Encryption for high-value cloud computations.
- Govern: Ensure your legal team understands that “encrypted processing” is the future of compliance.