Beyond the Perimeter: Mastering Security with Cloud-Native Application Protection Platforms (CNAPP)
Introduction
The digital transformation has reached a point of no return. As organizations decommission their last physical servers in favor of elastic, distributed environments, the old ways of “bolting on” security are failing. We have entered the era of the CNAPP.
In 2026, securing the cloud isn’t about managing a firewall; it’s about managing an ecosystem. A CNAPP is the “Single Pane of Glass” that allows security teams to see, protect, and govern every layer of their cloud journey—from the first line of code to the live production environment.
1. The Fragmentation Problem: Why Traditional Security Failed
Before CNAPP, cloud security was a “tool sprawl” nightmare. Companies would buy one tool for their containers, another for their infrastructure-as-code (IaC), and a third for their runtime monitoring. These tools didn’t talk to each other, resulting in “siloed” data and thousands of duplicate alerts that overwhelmed security analysts.
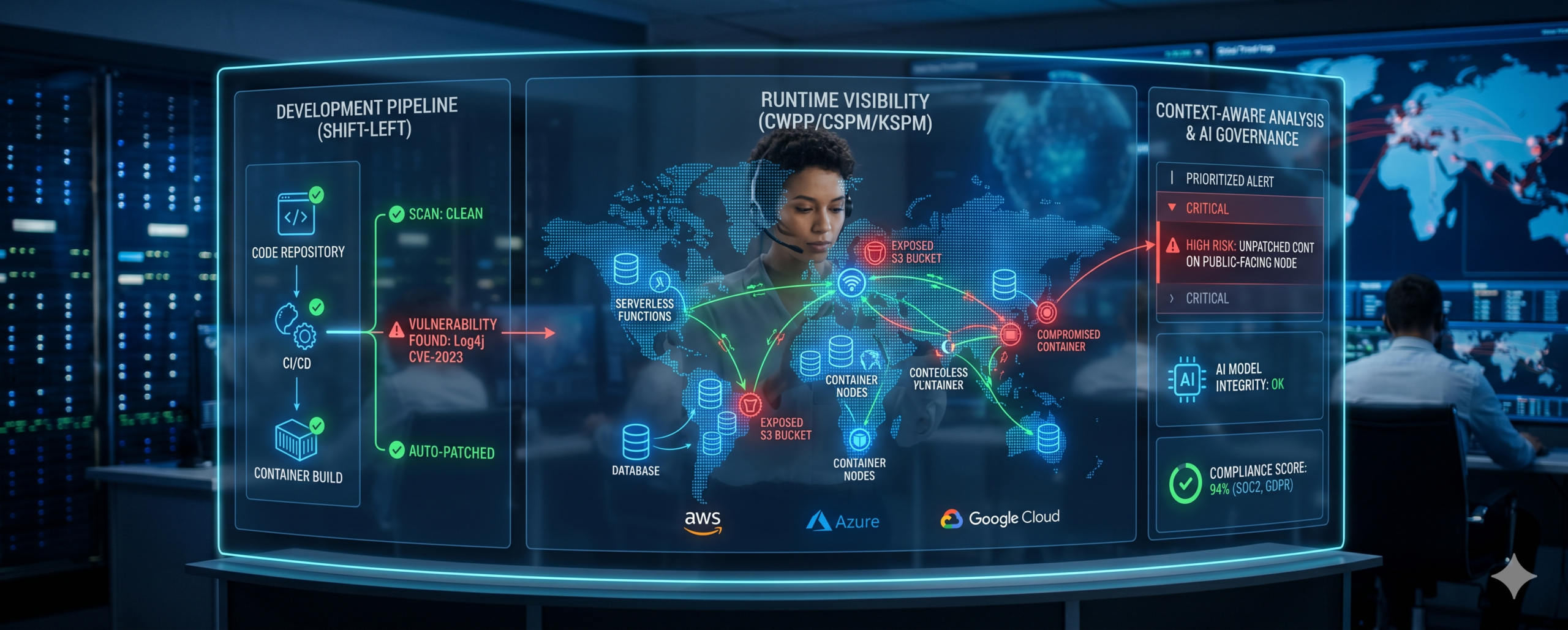
A CNAPP solves this by consolidating three critical pillars into one architecture:
- CWPP (Cloud Workload Protection Platform): Protects the actual “machines” (containers, serverless functions).
- CSPM (Cloud Security Posture Management): Scans for misconfigurations (like an accidentally public S3 bucket).
- KSPM (Kubernetes Security Posture Management): Specifically secures the complex orchestration of containerized apps.
2. Shift-Left: Securing the Code Before it Breathes
One of the most powerful features of a CNAPP is its ability to “Shift Left.” Traditionally, security only checked for problems after an app was “live.” If a vulnerability was found, it was expensive and slow to fix.
With CNAPP, security is integrated directly into the developer’s workflow. As a developer writes code, the CNAPP scans the Infrastructure as Code (IaC) templates for security flaws. If a developer accidentally leaves a database port open in their configuration, the CNAPP flags it before the code is ever deployed.
3. Context is King: Reducing Alert Fatigue
The greatest enemy of a modern SOC (Security Operations Center) is noise. A traditional tool might flag 500 “High Priority” vulnerabilities. A CNAPP uses Context-Aware Analysis to tell you which ones actually matter.
For example, a standard scanner might flag an unpatched library in your system. A CNAPP looks deeper and says: “Yes, this library is unpatched, but it is not connected to the internet and has no sensitive data access. However, this OTHER vulnerability is on a public-facing server with admin privileges—fix this first.” This prioritization saves teams hundreds of hours of manual work.
4. The Future: Agentless Visibility and AI Governance
As we look toward 2027, CNAPPs are evolving to become “Agentless.” Instead of installing heavy software on every server (which slows down performance), CNAPPs take “snapshots” of the environment to identify threats with zero impact on the application’s speed.
Furthermore, we are seeing the integration of AI Governance within CNAPP. As businesses deploy their own AI models in the cloud, CNAPPs now monitor those models to ensure they aren’t leaking private data or being “poisoned” by malicious prompts.
Conclusion: One Platform to Rule the Cloud
The shift to cloud-native isn’t just a change in where your data sits; it’s a change in how you think about risk. By adopting a Cloud-Native Application Protection Platform, you stop chasing individual fires and start managing a resilient, self-securing infrastructure.
At Right to Connect, we help organizations transition from fragmented “point solutions” to a unified CNAPP strategy. We ensure that your developers can move fast, while your security team sleeps soundly, knowing that every container, function, and line of code is being watched by a single, intelligent eye.
Why Your Business Needs a CNAPP Today:
- Cost Reduction: Consolidate multiple expensive security licenses into one.
- Developer Velocity: Catch bugs in the “dev” phase, not the “disaster” phase.
- Full Visibility: See your entire cloud footprint (AWS, Azure, Google Cloud) in one window.
- Compliance: Automatically generate reports for SOC2, HIPAA, or GDPR compliance across all cloud assets.