The Convergence Crisis: Securing the Invisible Bridge Between Internet of Things (IoT) and Operational Technology (OT)
Introduction
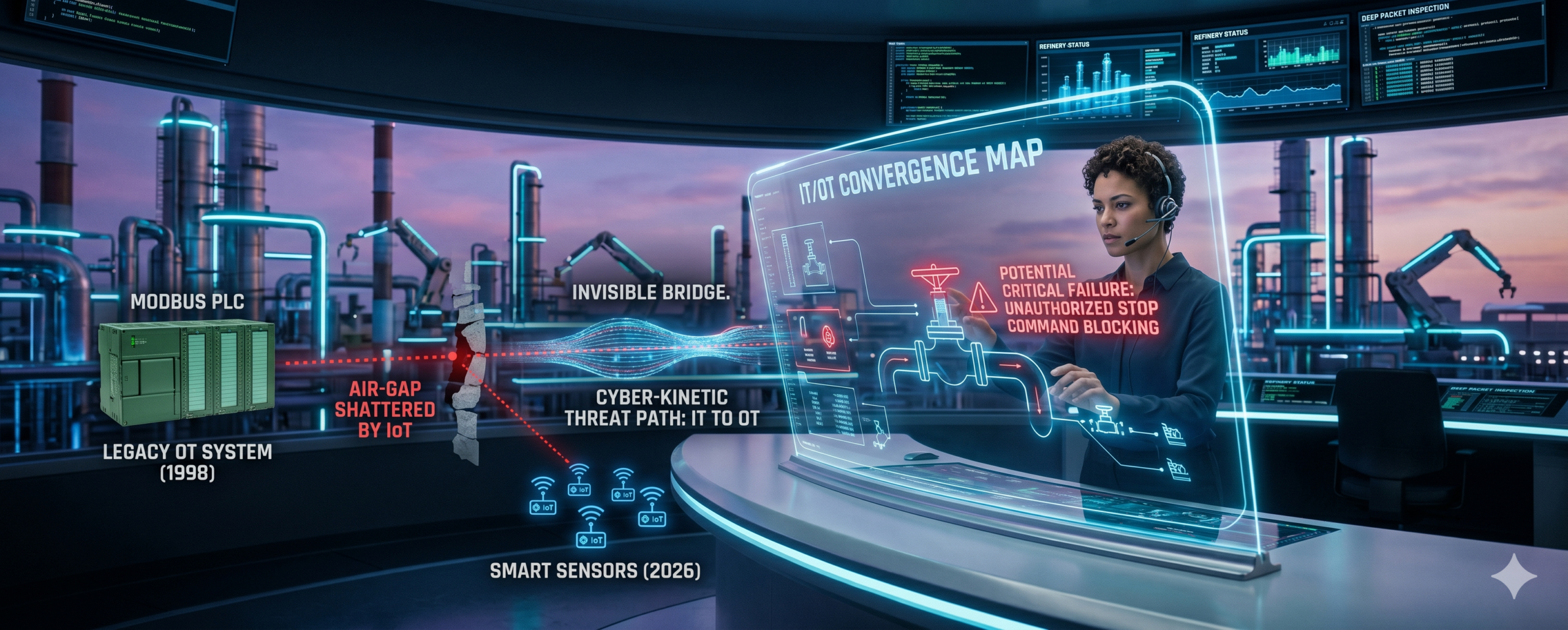
For decades, a thick wall separated the world of Information Technology (IT) and Operational Technology (OT). While IT teams managed data, emails, and servers, OT teams managed the physical world: power grids, water treatment sensors, assembly lines, and chemical refineries. These systems were “air-gapped”—physically disconnected from the internet.
However, the rise of the Industrial Internet of Things (IoT) has shattered that wall. In 2026, the bridge between digital bits and physical atoms is fully built, creating a massive new frontier for cyber warfare.
1. Defining the Convergence: When Data Meets Machinery
The convergence of IoT and OT allows companies to use real-time data to optimize physical processes. Sensors (IoT) now monitor the heat, vibration, and pressure of heavy machinery (OT), feeding that data into AI models to predict failures before they happen.
While this increases efficiency by up to 40%, it also means that a hacker in a remote location can now potentially control a physical valve, a robotic arm, or a city’s power distribution. The “air gap” is gone, replaced by a permanent, high-speed connection that attackers are eager to exploit.
2. The Stakes: Kinetic Cybersecurity
In traditional IT security, the worst-case scenario is a data breach or financial loss. In OT security, we face “Kinetic” consequences—physical damage, environmental disasters, or loss of human life.
The Vulnerability of Legacy Systems
Most OT infrastructure was built 20 to 30 years ago, long before cybersecurity was a design requirement. These systems use “insecure by design” protocols that do not require passwords or encryption. When you connect a 1995-era water pump controller to a 2026-era IoT cloud, you are essentially giving a vintage car a jet engine without upgrading the brakes.
Attackers target these “dumb” devices because they lack the processing power to run modern antivirus software. Once an attacker gains access to a single smart lightbulb or thermostat on the network, they can move laterally into the industrial controllers that run the entire facility.
3. The New Threat Actor Profile
We are seeing a shift in who is attacking these systems. While ransomware gangs still target factories for profit, State-Sponsored Actors are increasingly “pre-positioning” themselves inside critical infrastructure.
The “Sleeper Cell” Strategy
Instead of immediately shutting down a power grid, attackers often install persistent backdoors. Their goal is not immediate disruption, but “strategic leverage.” By staying hidden for months or years, they ensure that in the event of a geopolitical conflict, they can disable a nation’s water or electricity with a single keystroke.
4. Building the Shield: A Unified Defense Strategy
Protecting converged environments requires a specialized approach that differs from standard IT security.
Micro-Segmentation
Since OT devices are often unpatchable, we must use Micro-Segmentation. This involves creating “security zones” around every physical machine. If a sensor in the warehouse is compromised, the segmentation prevents the threat from moving to the main production line.
Protocol-Aware Deep Packet Inspection (DPI)
Standard firewalls don’t speak “industrial.” Professional teams must use DPI tools that understand industrial languages like Modbus or BACnet. These tools can recognize the difference between a “Read Data” command (normal) and a “Stop Motor” command (dangerous) and block the latter in real-time.
Passive Monitoring
In OT, you cannot “active scan” a device. If you ping a legacy controller too hard, it might crash, shutting down the entire factory. Defense must be passive, listening to network traffic silently and using AI to detect anomalies without ever touching the machinery itself.
5. The Future: AI-Driven Industrial Resilience
As we look toward 2027, the focus is shifting from “prevention” to “Industrial Resilience.” This means using digital twins—virtual copies of a factory—to simulate attacks and test defenses before they happen in the real world.
Conclusion: Securing the Physical Foundation
The convergence of IoT and OT is inevitable and necessary for a modern economy. However, it requires a new breed of cybersecurity professional—one who understands both the line of code and the line of production.
By implementing Zero Trust for Industry, professional teams can ensure that the “invisible bridge” between the internet and our physical world remains a path for progress, not a gateway for disaster. At Right to Connect, we specialize in hardening these physical foundations, ensuring that your machinery remains under your control, and your community remains safe.
Key Takeaways for Executives:
- Physical Risk: OT security is about safety, not just data.
- Visibility: You must map every IoT sensor to understand your attack surface.
- Passive Defense: Never use standard IT scanning tools on OT equipment.
- Segment Now: Isolate your industrial machines from your office Wi-Fi immediately.